ICO Fines Capita £14 Million Over 58-Hour Delay in Cyber Response
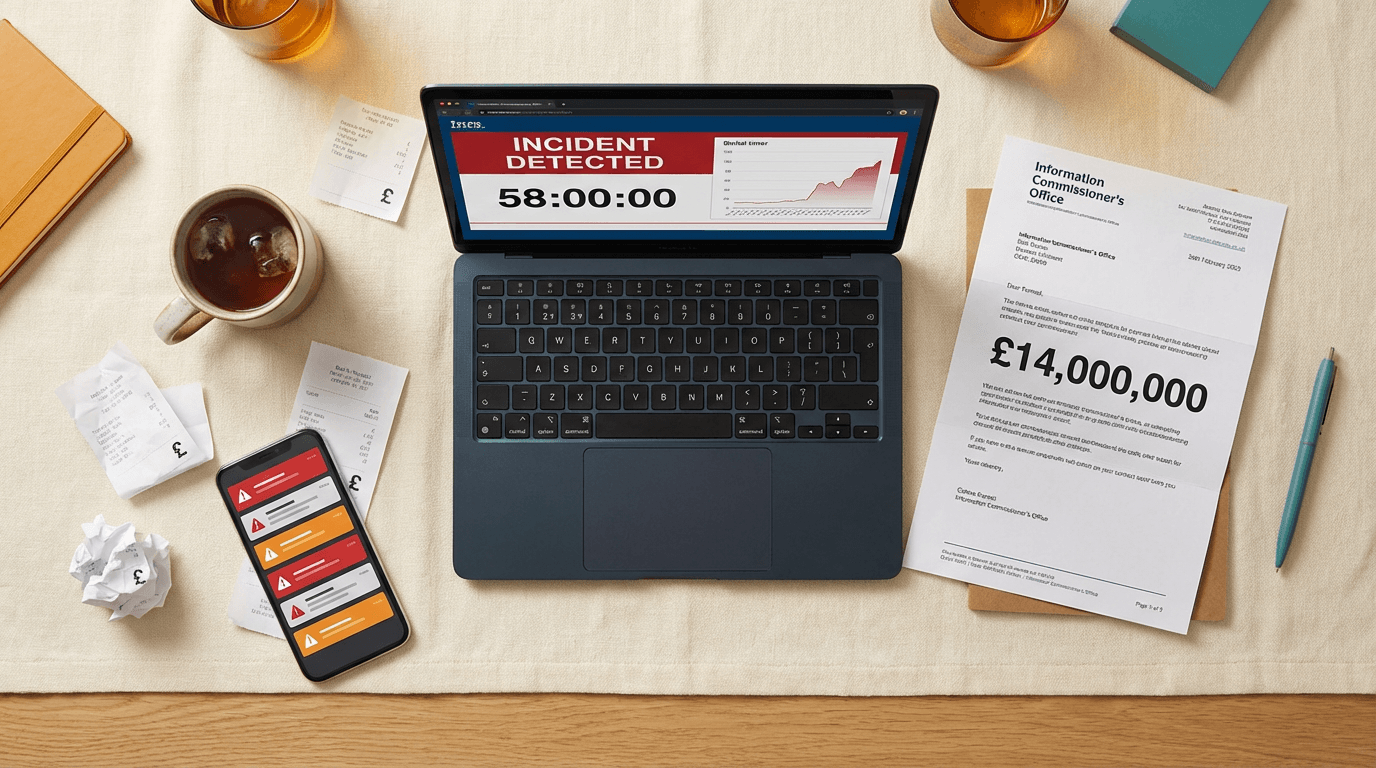
The UK Information Commissioner's Office fined outsourcing giant Capita £14 million this week for a 2023 cyber attack that exposed the personal and financial data of 6.6 million people. The penalty highlights a brutal reality for UK businesses: having security monitoring in place is useless if your team ignores the alarms. The breach stemmed from a single compromised employee device that triggered a high-priority alert within 10 minutes, yet was left unquarantined for 58 hours.
The £14 million cost of a 58-hour delay
In October 2025, the ICO issued a combined £14 million fine to Capita plc and its subsidiary, Capita Pension Solutions Limited, for failing to protect personal data during a March 2023 ransomware attack. According to RPC, an employee unintentionally downloaded a malicious file onto a work device.
The critical failure wasn't the initial infection. Capita's security systems actually worked, raising a high-priority alert within 10 minutes. But the company failed to quarantine the infected device for 58 hours. During that window, attackers exploited the system, escalated their administrative privileges, and moved laterally across the network.
They ultimately extracted nearly one terabyte of data, including sensitive pension records and financial details. The ICO originally considered a penalty of up to £58 million, according to a recent data protection update. Capita managed to reduce the final figure to £14 million by agreeing to a voluntary settlement, admitting liability, and waiving its right to appeal. The regulator specifically called out Capita's failure to build a tiering model for administrative accounts, which allowed the hackers to roam freely once inside.
Why alert fatigue is your biggest liability
Most SME leaders think about cyber security as a wall. You buy the software, you set up the firewall, and you assume you're protected. The Capita fine proves the ICO thinks about security as a stopwatch.
If you process financial data or act as a data processor for other businesses, the regulator doesn't just care that you were breached. They care exactly how many minutes it took you to react. A 58-hour delay, which is essentially a Friday afternoon to a Monday morning, is now officially grounds for a massive penalty.
I see too many 50-person businesses spending their entire IT budget on detection tools while completely ignoring their response protocols. If your system flags a critical threat at 8 PM on a Saturday, who gets the notification? If the answer is an unmonitored inbox, you're carrying the exact same structural risk that just cost Capita £14 million.
The ICO also made a point of punishing Capita for failing to separate administrative privileges. If a junior employee's laptop gets compromised, the attacker shouldn't be able to use that foothold to access your core financial databases. Flat network structures are cheap to run, but they're indefensible when the regulator comes knocking.
Three things to check
- Test your weekend response plan. Ask your IT lead or managed service provider exactly what happens if a critical ransomware alert fires at 2 AM on a Sunday. If the protocol relies on someone checking their phone by chance, you need a formal on-call rota or an automated quarantine rule.
- Audit your admin accounts. You need to restrict lateral movement. Enforce a tiering model for administrative access so that a compromised standard user account can't be used to access sensitive financial data or core servers.
- Automate device isolation. Modern endpoint detection tools allow you to automatically disconnect a device from the corporate network the moment a high-severity threat is detected. Turn this feature on for all staff laptops. It's better to accidentally lock an employee out of their email for an hour than to give a hacker a 58-hour head start.
Get our UK AI insights.
Practical reads on AI for UK businesses — teardowns, how-to guides, regulatory news. Unsubscribe anytime.
Unsubscribe anytime.